Brazilian cybercrime attacks Portugal and Spain
The company Check Point Software, Specializing in cybersecurity solutions at a global level, it disclosed that the company’s researchers detected and blocked more than 100 cyber attacks that targeted countries in Latin America and the Iberian Peninsula. The attack involved an evolved version of a banking trojan named Mekotio.
The researchers believe that Mekotio is authored by Brazilian cybercrime groups that rent to other groups access to their attack tools. The latter are responsible for distributing the trojan and laundering funds. Developed to affect Windows computers, Mekotio is known to use spoofed emails that mimic legitimate associations. After a victim is infected, the banking trojan remains hidden, waiting for users to log into electronic bank accounts, silently collecting their credentials.
In July of this year, Spanish authorities arrested 16 suspects on charges of laundering funds stolen through the banking trojan Mekotio, among others. The recent edits of the Check Point Research reveal that the malicious agents behind Mekotio are still active, distributing a new version of Mekotio with new and improved stealth and evasion features.
According to cyber attacks detected by Check Point Research, Mekotio’s target countries include Brazil, Chile, Mexico, Peru, Portugal and Spain.
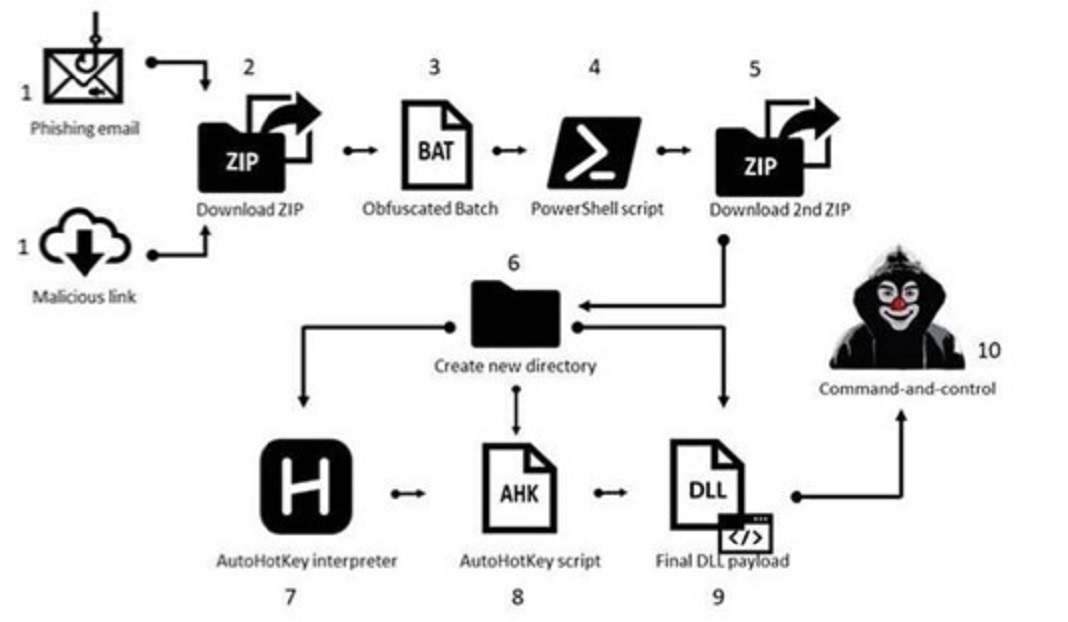
How new Mekotio media are processed
The infection starts and is distributed with a phishing email, written in Spanish, containing a link to a zip file or a zip file as an attachment. The message prompts the victim to download and extract the contents of the zip. Email messages identified by Check Point Research alleged an alleged “pending submission of digital tax receipt”. When as killed click on the link in the email, a malicious zip file is downloaded.
New theft and evasion techniques
One of Mekotio’s key features is its modular design, which gives attackers the ability to change a small part of the whole and thus avoid detection. Furthermore, Mekotio uses an old encryption method, “replacement cipher”, to obfuscate the file content and hide the first attack module. This simple obfuscation technique allows it to go unnoticed by most antiviruses. Furthermore, Mekotio’s malicious agents use a new version of a commercial tool called “Themida”, which involves the payload with sophisticated encryption, anti-debug and anti-monitoring.
“Although the Spanish Civil Guard announced the arrest of 16 people involved in the distribution of Mekotio in July 2021, it appears that the group behind the malware is still active. It is clear to us that they have developed and distributed a new version of banker Mekotio which has stealth features and much more effective evasion techniques. There is a very real danger that banker Mekotio will steal usernames and passwords in order to gain entry into institutions. Furthermore, the arrests have stopped the activity of Spanish groups, but not the main cybercrime groups behind the Mekotio. We know a few things about the malicious agents behind Mekotio, which operates out of Brazil and collaborates with European criminals to distribute malware, indicated Kobi Eisenkraft, Malware Research and Protection Team Leader from Check Point Software
Kobi Eisenkraft added that malicious agents behind Mekotio:
- They like to use a multi-stage delivery infrastructure so they don’t get detected
- Primarily use phishing emails as the first infection vector
- Use Microsoft and Amazon cloud environments to host malicious files
That’s why the expert recommends “people in Mekotio’s target regions to use two-factor authentication whenever it is available and be careful with similar domains, misspellings in emails or websites, and unknown email senders”.
the advice of Check Point Software to keep yourself protected are:
1 Look out for similar domains, misspellings in emails or websites, and unknown senders.
two Be wary of files received via email from email addresses you don’t know, especially if they incite you to take suspicious action.
3 Make sure you order goods from security sources. To do this, do not click on promotional links in emails. Instead, do an organic Google search.
4 Beware of special offers and buying opportunities that sound too good to be true.
5 Do not reuse passwords across different accounts and platforms.




